©2021 Reporters Post24. All Rights Reserved.
The North Korean ‘Lazarus’ hacking group targeted employees of an aerospace company located in Spain with fake job opportunities to hack into the corporate network using a previously unknown ‘LightlessCan’ backdoor.
The hackers utilized their ongoing “Operation Dreamjob” campaign, which entails approaching a target over LinkedIn and engaging in a fake employee recruitment process that, at some point, required the victim to download a file.
The employee did so on a company’s computer, allowing the North Korean hackers to breach the corporate network to conduct cyber espionage.
ESET investigated the incident and could reconstruct the initial access and retrieve components of Lazarus’ toolset, including a previously undocumented backdoor, which they named ‘LightlessCan.’
Lazarus attack chain
The Operation Dreamjob attack reconstructed by ESET started with a LinkedIn message by the Lazarus actor pretending to be a recruiter from Meta (Facebook) named Steve Dawson.
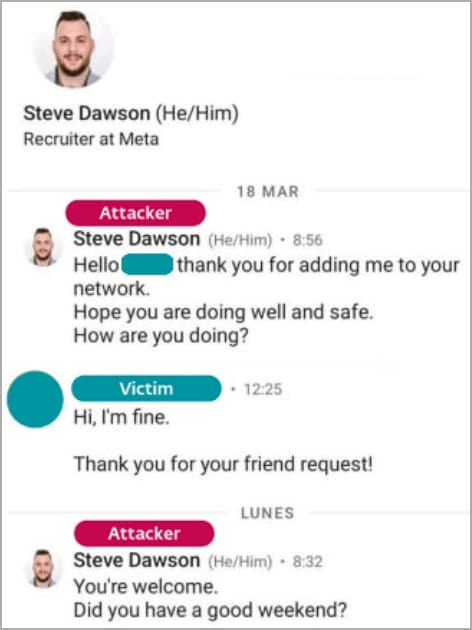
Source: ESET
At later stages of the discussion, the victim was asked to prove their proficiency in C++ programming by downloading some quizzes that were shared as executables within ISO files.
Once those executables were launched, an additional payload from the ISO images was silently dropped onto the victim’s machine via DLL side-loading (mscoree.dll) using a legitimate program (PresentationHost.exe).
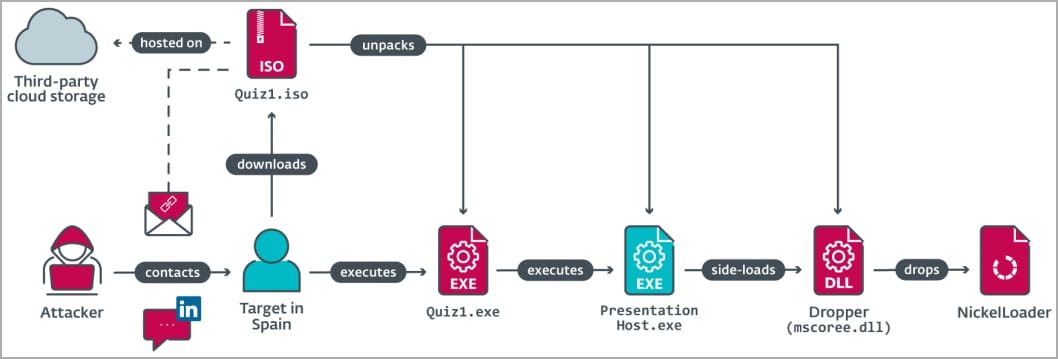
Source: ESET
That payload is the NickelLoader malware loader, seen deploying two backdoors, a variant of BlindingCan with toned-down functionality (miniBlindingCan) and LightlessCan.
The commands supported by miniBlindingCan are:
- Send system details (computer name, Windows version, code page).
- Update communication interval (value from C2 server).
- Stop command execution.
- Send 9,392-byte configuration to C2 server.
- Update encrypted 9,392-byte configuration on file system.
- Wait for the next command.
- Update communication interval (from configuration).
- Download & decrypt files from C2 server.
- Execute the provided shellcode.
The LightlessCan backdoor
ESET says LightlessCan is a successor to BlindingCan, based on source code and command ordering similarities, featuring a more sophisticated code structure, different indexing, and enhanced functionality.
The version sampled from the attack on the Spanish aerospace organization is 1.0, featuring support for 43 commands. However, ESET says there are another 25 commands in the code which have not been implemented yet.
The malware replicates many native Windows commands like ping, ipconfig, netstant, mkdir, schstasks, systeminfo, etc., so it can execute them without appearing in the system console for better stealthiness against real-time monitoring tools.
Since those commands are closed-source, ESET comments that Lazarus has either managed to reverse engineer the code or drew inspiration from the open-source versions.
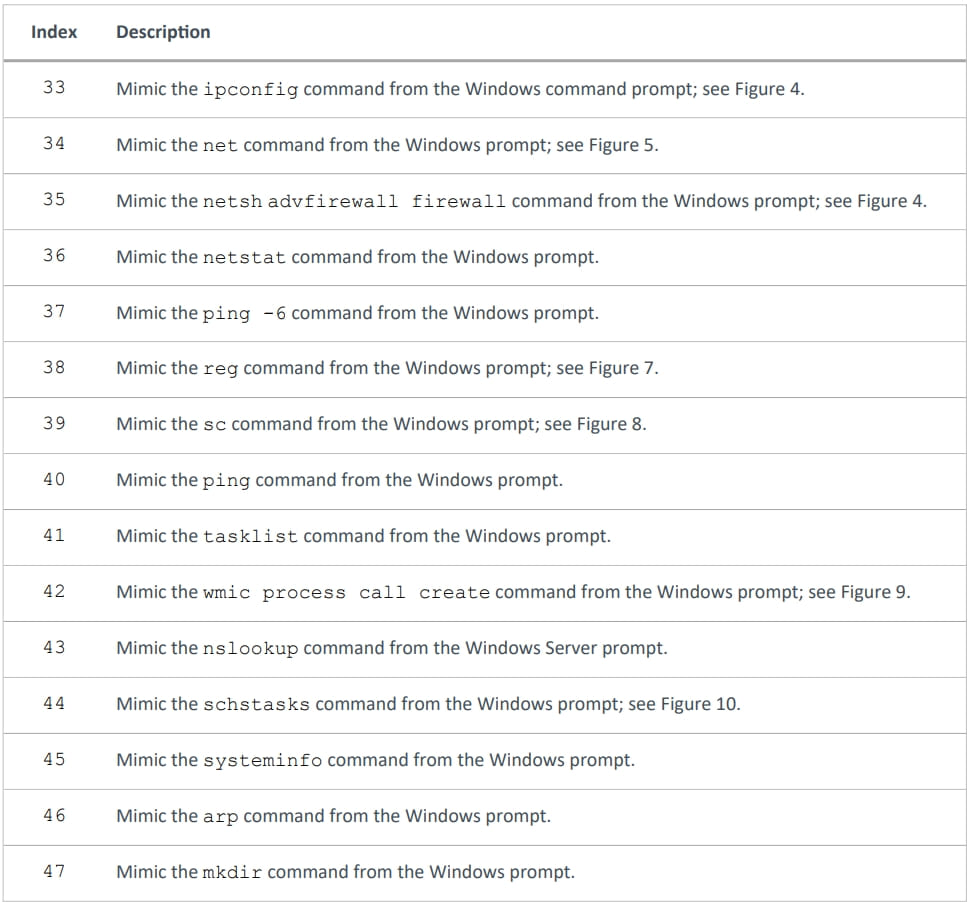
Source: ESET
Another interesting aspect reported by ESET is that one of the LightlessCan payloads they sampled was encrypted and could only be decrypted using a key dependent on the target’s environment.
This is an active protection measure to prevent outside access to the victim’s computer, for example, by security researchers or analysts.
This discovery underscores that Lazarus’ Operation Dreamjob is not solely driven by financial objectives, such as cryptocurrency theft, but also encompasses espionage goals.
Also, the introduction of a new sophisticated payload, the LightlessCan, is a concerning development for organizations that might find themselves in the cross-hairs of the North Korean threat group.


